Essay on Data and Networking
Number of words: 1535
Introduction:
The topologies of a network involve the configuration of nodes & connections in a certain method or pattern. In other terms, network topologies refer to how the system components which enable communication among network elements are organized in order to decrease mistakes, increase bandwidth, safeguard the system, & so on. In today’s environment, networking & data are critical for any company’s performance and ability to compete. Xerlasian University, a prominent higher ed institution, seems to be in the process of establishing a new branch in Australia. As a data & networking expert, I would’ve been responsible for designing, integrating, & tracking the efficient approach & implementation utilizing the TCP/IP framework (Transmission Control Protocol/Internet Protocol), network configuration framework, & numerous network equipment such as hubs, routers, &servers. In this work, I conducted an analytic investigation of many fundamental topologies, providing us with a brief overview of topology & its characteristics at Xerlasian University (Nedić, et.al., 2018, P. 953-976).
Discussion:
Current Network at Xerlasian University:
Using different networking types & stack protocols, Xerlasian University might use a relatively basic data flow approach. On campuses, this network system might be a Local Network (LAN) that followed the Star architecture. The system gives customers in 2 or even more buildings, as well as the outdoor spaces surrounds those structures, with wireless Net or LAN connectivity. The campus networks are often found on a university’s campus, although the same architecture & layout can be used for other reasons. The college building grounds were not interconnected a couple of years prior (Nedić, et.al., 2018, P. 953-976). There was no bound together Internet association, and every unit was answerable for its own organizations. A huge work has done, and a various leveled network engineering Layer 2 exchanged, is presently is utilized. Web access is given through 1 switch as it were. The college has 2 layers various leveled engineering which are:
- One is Core layer which give fine transportation among destinations and likewise gives high Routing execution.
- Second is Distribution layer which gives network identified with strategies and control splitting line between Core and access layers.
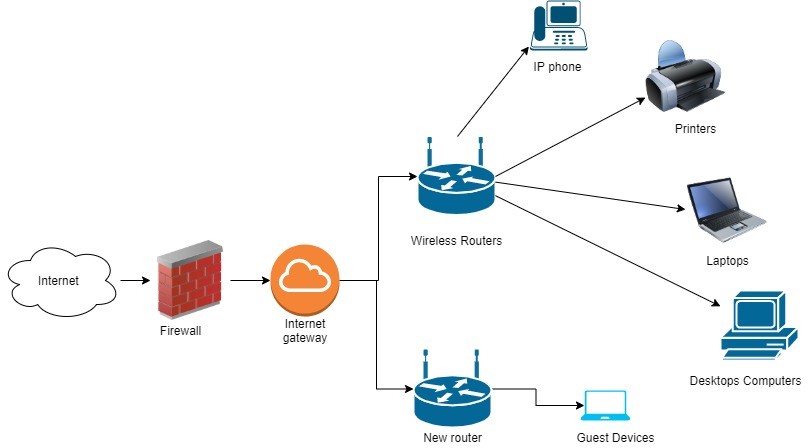
Figure 1: Network Topology
Current networks constraints:
Network topology Recommendation, comparison, and factors
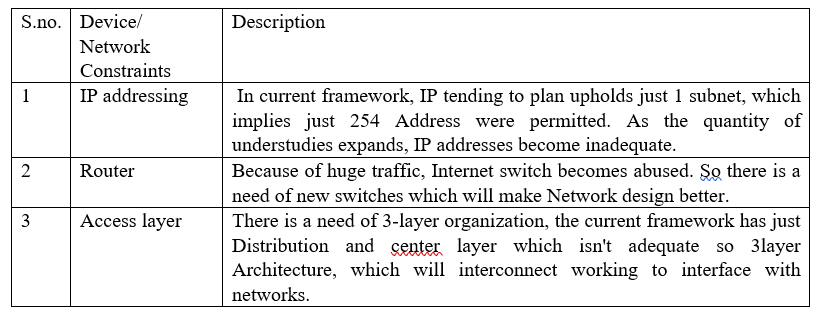
Network topology is a geometrical depiction of how devices are related to one another. Mesh, Bus, Star, Ring, & Hybrid are 5 types of topologies. The manner pcs or stations are joined together in a network connection is referred to as topology(Nedić, et.al., 2018, P. 953-976).
A network infrastructure suitable for a Xerlasian campus is provided by this star configuration. It requires a low initial cost & enables adding new devices to the network simple. A technique that utilizes a star topology is much more dependable and efficient. The bus architecture is a communication topology that is not suitable for use on Xerlasian university grounds. Whenever the foundation, or backbone, of a system break, the overall system collapses. The wires are also limited in length, & their efficacy is slow. A centralized switch or hub is utilized to link all of the elements in this architecture (Nedić, et.al., 2018). The gadgets or individuals really aren’t linked to one another, yet direct traffic between them is possible. An engaged hub in an effective star network typically has the capacity to inhibit echo-related issues (Yuksel&Altunay, 2020, P. 43).
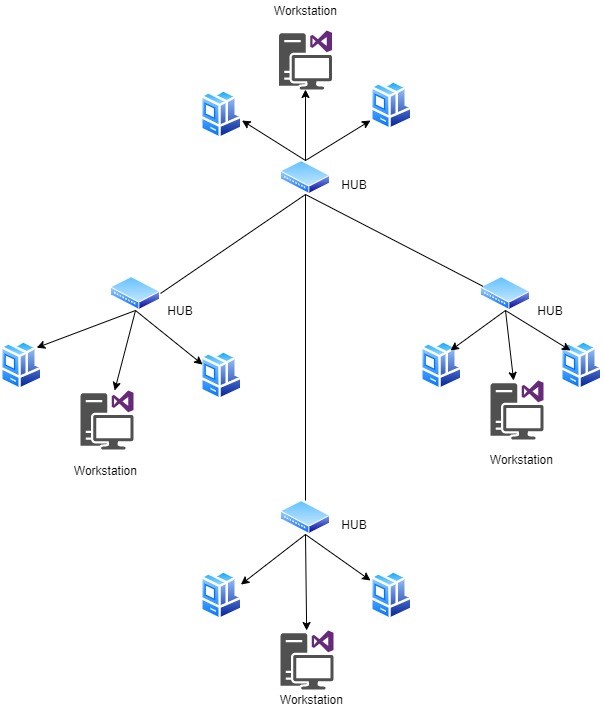
Figure 2: Star Topology for Xerlasian university
Benefits:
- system/Network faults are simple to diagnose.
- Excellent performance.
- Scalable & simple to start up & expand.
- Using a hub to connect several cable kinds in same networks.
Drawbacks:
- Rely only on a single hub.
- Installation costs a lot of money
Redesigning the network:
Following are the progressions which must be done in grounds:
- Wirelessly access of web in every one of the structures of grounds.
- Reduce deals from switches and work on the switch and IP tending to.
- Changes in Security and exhibitions boundary.
Several other architecture concepts are included in the text, but layering is not one of them. It informally describes a four-layer structure, with titles rather than quantities for the layers:
- The application layer is only the region where applications produce client data and move it with the other applications on same different hosts. The crucial, lower layers offer capacities to the projects, or cycles, especially the Transmission Control convention, that gives trustworthy or defective pipelines to different techniques. The proposed system, similar to the customer worker worldview and shared availability, characterizes the associations sidekicks. All more elevated level innovations, as SMTP, SSH, FTP, and HTTP, execute at this level. Ports, that are fundamentally applications, are utilized to address exercises ((Nedić, et.al., 2018, P. 953-976).
- The Transport Layer handles have to-have cooperation with the equivalent or particular hosts, just as neighborhood and distant associations split by switches. It goes about as a course for applications’ correspondences prerequisites. UDP is a basic vehicle convention that conveys conflicting organization bundles. Stream control, associations arrangement, and information move unwavering quality are totally given by the Tcp Protocol. (Lin et al., 2017, P. 3993-4013).
- The Internet protocol is responsible for sending and receiving packets of data throughout different nodes. It offers a normalized interchanges interface which hides the organization framework parts’ engineering (format). Subsequently, it is otherwise called layer which empowers web network, and its the hindrance which characterizes and fosters the Internet. This layer specifies the TCP/IP protocols suite’s addresses & routing mechanisms. The Internet Layer that specifies Ip’s is the most important communication in this context. Its role in routing is to deliver network packets to next IP router with accessing the network that really is closer to the target data endpoint (Yuksel& Altunav, 2020, P. 43).
- The Link layer determines the organizations systems utilized by hosts to collaborate over a nearby arranged connection without need for switches. The standards that used define the local networked architecture, as well as the interfaces required to transmit Internet layer network packets to next-neighbor servers, are included in this stack.
Even before OSI framework was created, the TCP/IP & the stacked protocol architecture were used. Ever since, this TCP/IP paradigm has indeed been contrasted to the Osi reference framework in textbooks & courses, creating confusion because of 2 concepts utilize differing ideas & aims, such as the significance of precise layering (Ochoa et al., 2017, P. 1-8).
Comparison between TCP-IP&OSI:
Mostly in TCP/IP paradigm, that only includes an application layered above transport layers, the top 3 levels inside the OSI framework, namely the applications layer, presenting layer, & session layer, really aren’t differentiated individually. While certain pure OSI technologies, like X.400, integrate them, a TCP/IP network system does not have to apply monolithic design well above transport stack (Bindschaedler, et.al, 2017, P. 115-125).
Conclusion:
I have conducted an analytical analysis of many fundamental topologies in this work, that provides us with a quick overview of topology & its characteristics. Different fundamental topologies are investigated for various criteria. To summaries, the Xerlasian campus networks will adhere to all TCP/IP prototype standards, & the system will be built to decrease redundancy & enhance smoothness in the campus network infrastructure. For various topologies, the setup reveals whether it is simple or complex. The term “cost” refers about whether or not a cabling is required. Flexible denotes whether or not the network has been modified. Failure is classified as high, low, or medium in terms of reliability. Expansion of topology depends on the acquisition of computers, & finally robust matches the capacity of each node’s connections (Bindschaedler, et.al, 2017, P. 115-125).
References
Bindschaedler, V., Rane, S., Brito, A. E., Rao, V., &Uzun, E. (2017, March). Achieving differential privacy in secure multiparty data aggregation protocols on star networks. In Proceedings of the Seventh ACM on Conference on Data and Application Security and Privacy (pp. 115-125).https://doi.org/10.1145/3029806.3029829
Lin, C., Cui, L., Coit, D. W., &Lv, M. (2017). Performance analysis for a wireless sensor network of star topology with random nodes deployment. Wireless Personal Communications, 97(3), 3993-4013.https://doi.org/10.1007/s11277-017-4711-4
Nedić, A., Olshevsky, A., &Rabbat, M. G. (2018). Network topology and communication-computation tradeoffs in decentralized optimization. Proceedings of the IEEE, 106(5), 953-976.https://doi.org/10.1109/JPROC.2018.2817461
Ochoa, M. N., Guizar, A., Maman, M., &Duda, A. (2017, October). Evaluating LoRa energy efficiency for adaptive networks: From star to mesh topologies. In 2017 IEEE 13th International Conference on Wireless and Mobile Computing, Networking and Communications (WiMob) (pp. 1-8). IEEE.https://doi.org/10.1109/WiMOB.2017.8115793
Yuksel, H., &Altunay, Ö. (2020). Host-to-host TCP/IP connection over serial ports using visible light communication. Physical Communication, 43, 101222.https://doi.org/10.1016/j.phycom.2020.101222